Number stations are mysterious broadcasts that appeared during the Cold War and still run today. You might hear sequences of numbers or tones that sound like random noise, but they’re actually secretly coded messages for spies. These signals use complex encryption and follow specific patterns, making them hard for outsiders to understand. They remain a fascinating part of espionage history, and if you keep exploring, you’ll discover even more intriguing details behind these covert transmissions.
Key Takeaways
- Number stations are covert radio broadcasts transmitting coded messages, primarily used during the Cold War for espionage communication.
- They feature repetitive number sequences or tones, often encrypted with complex cryptography like one-time pads.
- These broadcasts are intentionally designed to be unrecognizable to the untrained, ensuring message secrecy and security.
- Many stations still operate today, highlighting their ongoing role in covert operations and intelligence exchanges.
- To the public, they appear as mysterious strings of numbers, fueling intrigue and cryptographic fascination.
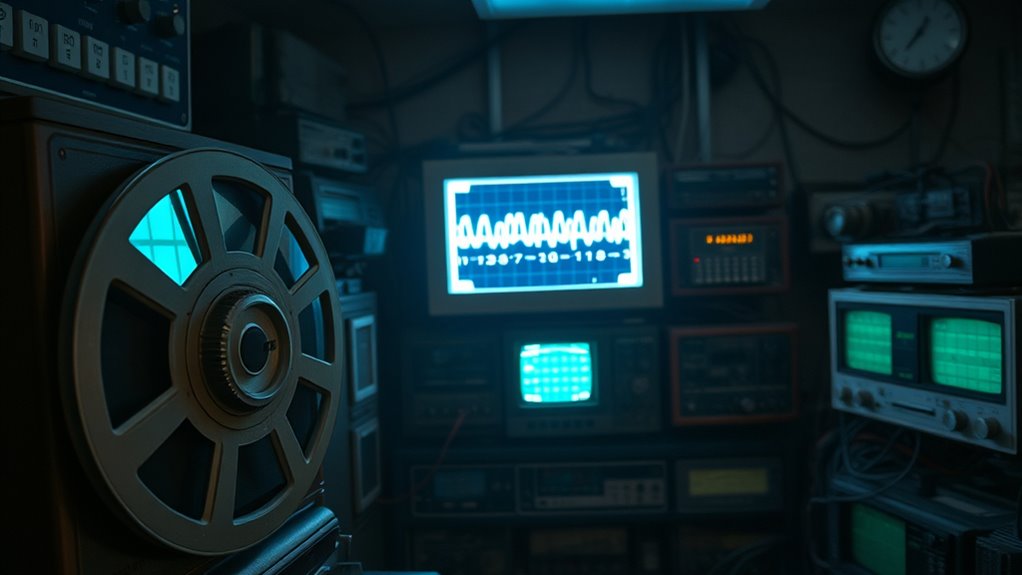
Have you ever wondered about those mysterious radio broadcasts that seem to transmit only a sequence of numbers? These are known as number stations, and they’ve fascinated listeners and cryptographers alike for decades. During the Cold War, governments used these broadcasts to secretly communicate with agents operating in foreign countries. The signals are simple: a voice or a computer-generated tone reads out a series of numbers, typically in a monotone voice or digital tone, and then the transmission ends. To the untrained ear, they might sound like random noise, but to those in the know, they are carefully coded messages.
Number stations broadcast coded messages using monotone voices or tones during the Cold War and beyond.
The secret behind these broadcasts lies in the sophisticated cryptography techniques used to encode the messages. The numbers aren’t just random; they’re encrypted with methods known only to the sender and intended recipients. This encryption guarantees listener privacy, preventing anyone intercepting the broadcast from understanding its true meaning. Cryptography techniques used in number stations range from simple substitution ciphers to more advanced algorithms, making it nearly impossible for outsiders to decipher the messages without the key. This layer of security is vital, especially considering the sensitive nature of the information being transmitted during tense political climates.
As a listener, you might wonder how these signals maintain their secrecy. The answer is in the encryption and randomization of the codes. Sometimes, the messages are transmitted with a one-time pad, an unbreakable encryption method if used correctly, which guarantees perfect listener privacy. The broadcasts often follow a pattern, like repeating the same series of numbers or using a specific frequency or time slot, so agents know when to tune in. The privacy of the communication is paramount, as it protects the identities and safety of spies and operatives. If anyone else intercepts the broadcast, they’ll only hear a string of unintelligible numbers, not the actual message.
Interestingly, many number stations still operate today, even after the Cold War’s end, hinting that their purpose remains relevant. The persistent use of these broadcasts underscores their effectiveness in covert communication. For enthusiasts and cryptographers, analyzing these signals offers insights into historical intelligence tactics and encryption methods. For the average listener, they remain a tantalizing mystery—an unsolved puzzle of espionage. Whether you see them as relics of Cold War paranoia or as ongoing tools for covert operations, one thing’s clear: number stations continue to intrigue, confound, and defy easy explanation.

COMICA VM30 Shotgun Microphone with Wireless Modes, USB C Digital Output, 75/150Hz, Super-Cardioid Universal Camera Microphone for Filmmakers, Vloggers - Wireless Mic for Camera, Smartphone, and PC
COMICA's Groundbreaking Wireless Shotgun Microphone: The COMICA VM30 features an integrated wireless module and supports both wired and...
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
Who Typically Operates These Number Stations Today?
Today, you’ll find that government agencies, like intelligence services or military units, typically operate these number stations. They use sophisticated cryptographic methods to encode messages, ensuring only authorized recipients can decode them. Station identification signals help listeners verify the station’s authenticity. These broadcasts maintain secrecy and secure communication channels, allowing operatives to exchange essential information discreetly. Despite modern tech, these stations still serve a covert purpose in intelligence operations.
Are There Any Confirmed Instances of Number Stations Transmitting False Information?
Like a whisper in the shadows, number stations have occasionally played with cryptographic deception, hinting at misinformation campaigns. While concrete proof remains elusive, some transmissions are suspected to have broadcast false information, serving as subtle psychological tactics. You can’t always tell if what you hear is truth or fiction, but these signals remind you that even in silent broadcasts, deception can be a powerful tool, lurking beneath the surface.
How Do Spies Decode Messages From These Stations?
You use cryptanalysis techniques to decode messages from these stations, focusing on patterns, frequency analysis, and known encryption methods. First, you isolate the signal, then analyze the structure, looking for recurring elements that reveal the encryption methods used. By applying these techniques, you can break the code, decipher the message, and understand the secret information being transmitted, all while adapting your approach as new encryption methods emerge.
What Equipment Is Needed to Listen to Number Stations?
Imagine stumbling upon a hidden signal—you’ll need a good radio receiver and an antenna to tune in. Start with a shortwave radio capable of picking up a wide range of frequencies, then connect an external antenna for better reception. Adjust the tuning until you hear those strange, coded broadcasts. With the right equipment, you can listen to the mysterious messages that have fascinated listeners for decades.
Have Any Governments Officially Acknowledged the Existence of These Stations?
Most governments haven’t officially acknowledged their existence, maintaining secrecy around number stations. You won’t find official recognition from any government confirming they operate these broadcasts, which fuels speculation and mystery. While some agencies might deny involvement, the lack of government acknowledgment keeps the true purpose and origin of these stations shrouded in secrecy. So, even today, their existence remains largely unconfirmed by official sources.

Movo X1-Mini Video Shotgun Mic for Camera - Supercardioid 3.5mm/USB-C Analog/Digital Camera Microphone for DSLR, iPhone and Android Smartphones, Computers - Compatible with Canon EOS, Nikon, Sony
UNIVERSAL COMPATIBILITY: This external microphone is perfect for iPhone, Android devices, cameras, camcorders, audio recorders, tablets, and laptops....
As an affiliate, we earn on qualifying purchases.
Conclusion
You’ve uncovered the mystery behind number stations, the silent messengers of the Cold War. You’ve seen how their coded messages, their secret signals, and their quiet broadcasts kept nations connected and secrets hidden. You’ve learned that these stations, mysterious and unchanged, continue to fascinate and puzzle us. You realize that their legacy lives on in curiosity, in secrecy, and in the enduring allure of the unknown, reminding us that some mysteries never truly fade away.

SENNHEISER Professional MKE 400 Directional On-Camera Shotgun Microphone with 3.5mm TRS and TRRS Connectors for DSLR, Mirrorless & Mobile , Connects with Auxiliary
Highly directional, super-cardioid shotgun microphone for isolated and enhanced in-camera audio for your video
As an affiliate, we earn on qualifying purchases.

Bestshoot Condenser Interview Microphone Photography Shotgun Mic for Video Camcorders DSLR DV Camcorder 11 inches/27cm Camera Microphone with Metal Holder, Anti-Wind Foam Cap XLR Cable
Professional Voice Pickups: this microphone shot gun has a cardioids pick-up pattern isolates the main sound source and...
As an affiliate, we earn on qualifying purchases.










